Programmable hardware TOTP token in a card format that fits any authentication system
Classic hardware TOTP token with SHA-1 algorithm support
Programmable hardware TOTP token in a key fob format that fits any authentication system
Classic hardware TOTP token with SHA-256 algorithm support
Programmable hardware TOTP token in a card format that fits any authentication system
Classic hardware TOTP token with SHA-1 algorithm support
Programmable hardware TOTP token in a key fob format that fits any authentication system
Classic hardware TOTP token with SHA-256 algorithm support
A free 2FA authenticator app with cloud backup, easy token transfer to a new phone, PIN and biometric authentication protection
Free OTP delivery with chatbots in messaging apps
Delivery of one-time passwords via SMS messages
Free delivery of one-time passwords via email
Free one-time passwords delivery via push notifications
A free 2FA authenticator app with cloud backup, easy token transfer to a new phone, PIN and biometric authentication protection
Free OTP delivery with chatbots in messaging apps
Delivery of one-time passwords via SMS messages
Free delivery of one-time passwords via email
Free one-time passwords delivery via push notifications
Guides
This guide outlines the process of setting up Protectimus multi-factor authentication (MFA or 2FA) for NetApp Virtual Desktop Service (VDS) using the RADIUS protocol.
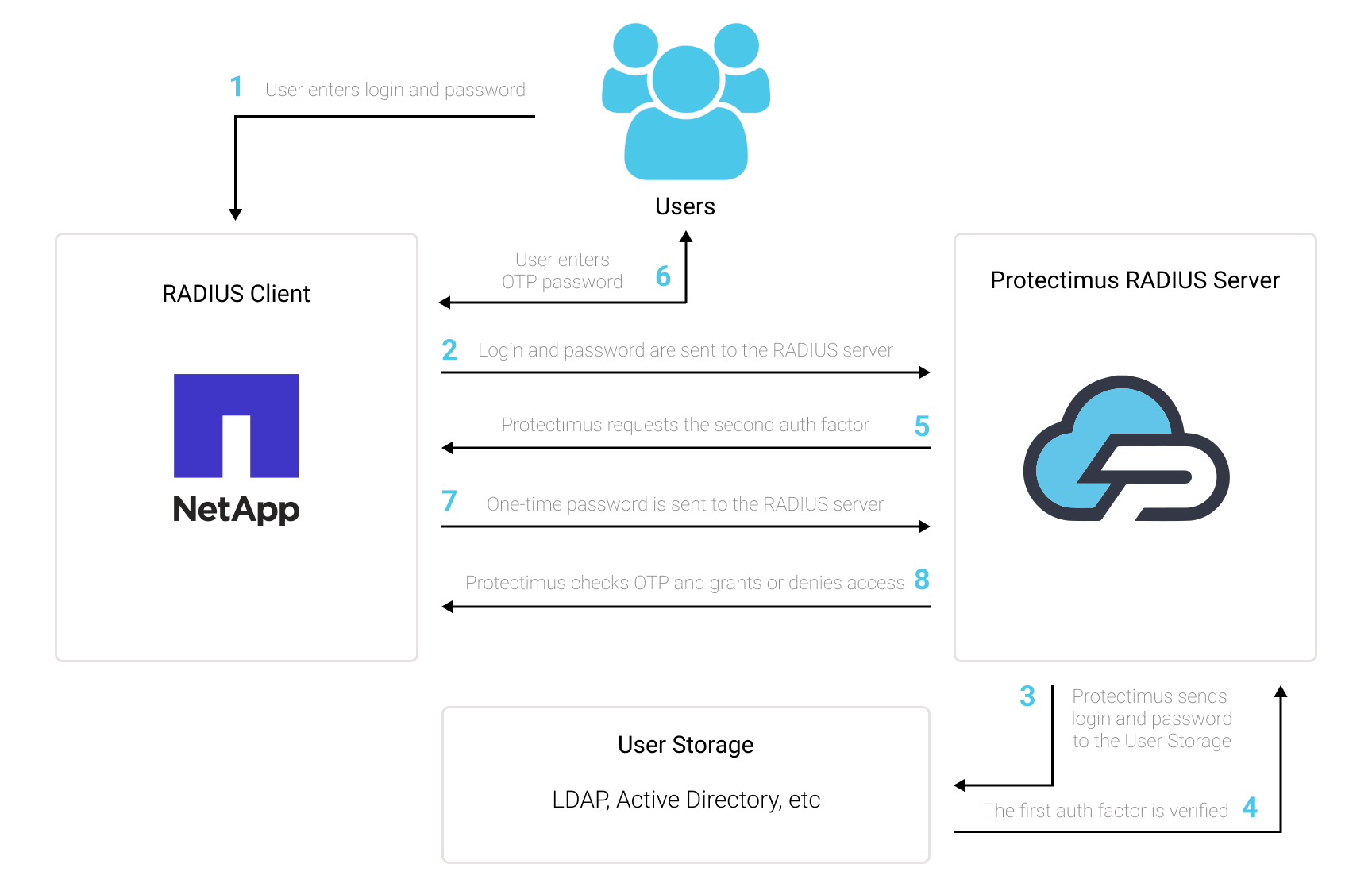
When integrating Protectimus two-factor authentication with NetApp Virtual Desktop Service via RADIUS, the Protectimus Cloud 2FA Service or On-Premise 2FA Platform serves as a RADIUS server through a dedicated connector known as Protectimus RADIUS Server. On the other hand, NetApp VDS operates as a RADIUS client.
Here’s how it functions: the Protectimus RADIUS Server connector forwards authentication requests from NetApp VDS to the Protectimus multi-factor authentication (MFA) server. Depending on the response received, access is either granted or denied.
Below, we offer an example of how to integrate Protectimus 2FA with NetApp Virtual Desktop Service for seamless NetApp VDS MFA.
You can set up multi-factor authentication (2FA) for NetApp VDS with Protectimus using the RADIUS protocol:
- Get registered with Protectimus SAAS Service or install the On-Premise 2FA Platform and configure basic settings.
- Install and configure Protectimus RADIUS Server.
- Add Protectimus as RADIUS Server for NetApp Virtual Desktop Service.
Detailed instructions for installing and configuring the Protectimus RADIUS Server for NetApp Virtual Desktop Service two-factor authentication using RADIUS are available in our Protectimus RADIUS Server Installation Guide for NetApp Virtual Desktop Service 2FA.
| Label | Come up with a name for your RADIUS server. |
| Hostname/Address | IP of server where the Protectimus RADIUS Server component is installed. |
| Authentication Port | Indicate 1812 (or whichever port you configured in the Protectimus radius.yml file when configuring Protectimus RADIUS Server). |
| Authentication type | PAP authentication is required. |
| Shared secret code | Indicate the shared secret you created in the Protectimus radius.yml file (radius.secret property) when configuring Protectimus RADIUS Server. |
| Server timeout (in seconds) | Set to 90 seconds. |
| Max attempts | This specifies how many times the authentication request should be sent. Set to 1. |
Integration of two-factor authentication (2FA/MFA) for your NetApp Virtual Desktop Service is now complete.
If you have other questions, contact Protectimus customer support service.
Protectimus Ltd
Carrick house, 49 Fitzwilliam Square,
Dublin D02 N578, Ireland
Ireland: +353 19 014 565
USA: +1 786 796 66 64
Protectimus Ltd
Carrick house, 49 Fitzwilliam Square,
Dublin D02 N578, Ireland
Ireland: +353 19 014 565
USA: +1 786 796 66 64


