Программируемый TOTP-токен в формате карты, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой SHA-1
Программируемый TOTP-токен в формате брелока, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой алгоритма SHA-256
Бесплатное 2FA-приложение с облачным бэкапом, удобным переносом токенов на новый телефон, PIN-кодом и биометрической защитой
Бесплатная доставка OTP с помощью чат-ботов в мессенджерах
Доставка одноразовых паролей через SMS
Бесплатная доставка OTP на email
Бесплатная доставка одноразовых паролей через push-уведомления
Guides
This Juniper VPN 2FA guide shows how to enable two-factor authentication (2FA / MFA) for Juniper Secure Access SSL VPN using the Protectimus Cloud 2FA Service or On-Premise 2FA Platform.
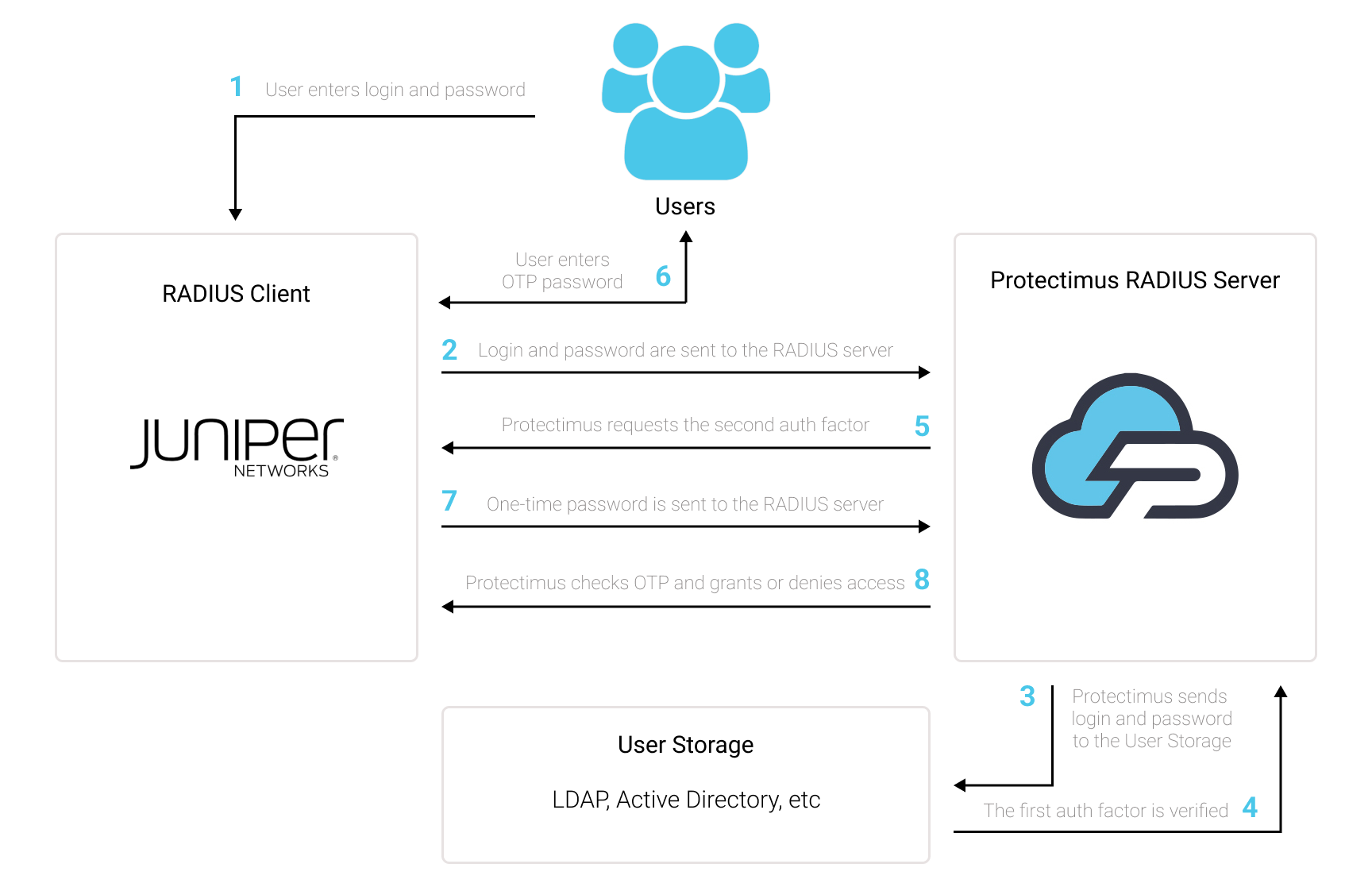
Protectimus integrates with Juniper Secure Access SSL VPN via RADIUS authentication protocol to add two-factor authentication (2FA) to VPN logins.
In this scenario, the Protectimus two-factor authentication solution for Juniper VPN 2FA performs as a RADIUS server, and the Juniper Secure Access SSL VPN takes the role of a RADIUS client. You will find the scheme of work of the Protectimus solution for Juniper VPN two-factor authentication below.
Two-factor authentication (2FA), also known as multi-factor authentication (MFA), is a must-have security measure for Juniper Secure Access SSL VPN. 2FA will protect Juniper VPN logins from such threats as phishing, brute force, data spoofing, social engineering, keyloggers, man-in-the-middle attacks, etc.
And this is how two-factor authentication for Juniper Secure Access SSL VPN works:
This way, to get access to the Juniper Secure Access SSL VPN account protected with two-factor authentication, the fraudster has to get access to two authentication factors that differ in their nature. That is quite a challenging task. Moreover, a time-based one-time password remains active only for 30 seconds, which makes hacking way more complecated and almost impossible.
You can set up Juniper VPN two-factor authentication (2FA) with Protectimus using the RADIUS protocol:
- Get registered with Protectimus SAAS Service or install the On-Premise 2FA Platform and configure basic settings.
- Install and configure Protectimus RADIUS Server.
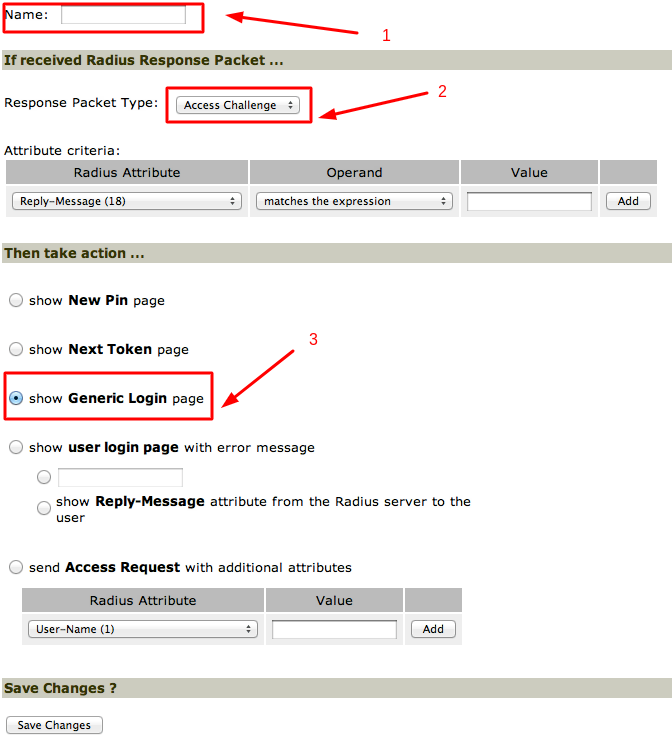
- Configure Juniper Secure Access SSL VPN authentication policies.
Detailed instructions for installing and configuring the Protectimus RADIUS Server for Juniper Secure Access SSL VPN using RADIUS are available in our Protectimus RADIUS Server Installation Guide for Juniper VPN 2FA.
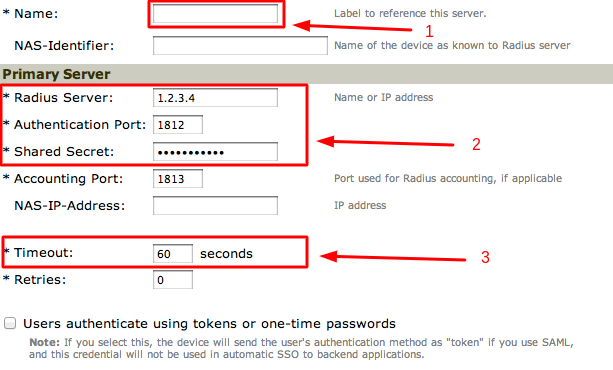
| Radius Server | IP of server where the Protectimus RADIUS Server component is installed. |
| Secret | Indicate the shared secret you created in the Protectimus radius.yml file (radius.secret property) when configuring Protectimus RADIUS Server. |
| Authentication Port | Indicate 1812 (or whichever port you configured in the Protectimus radius.yml file when configuring Protectimus RADIUS Server). |
| Timeout | Set to 60 seconds. |
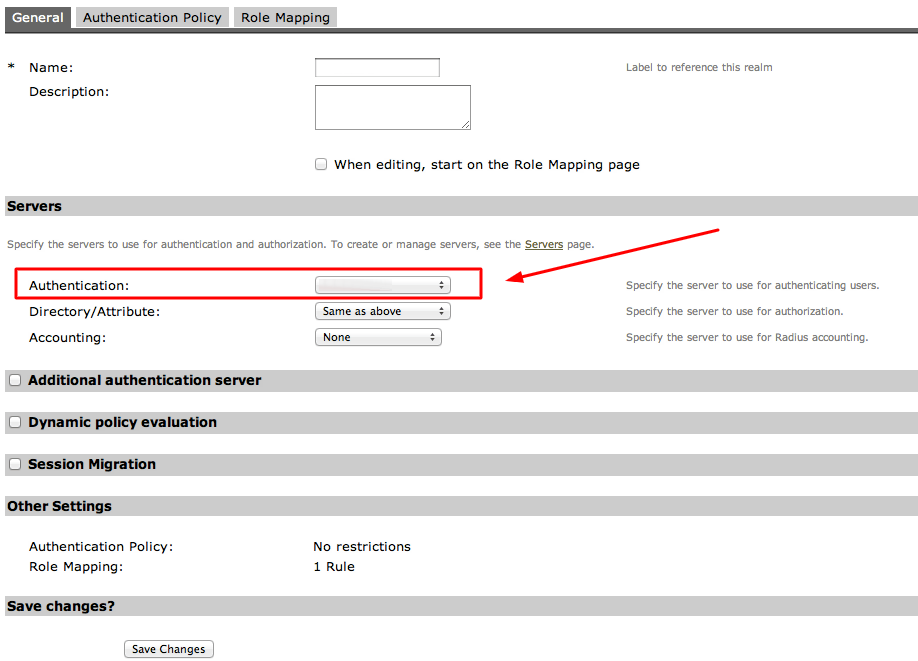
To add 2FA to a user realm:
Integration of two-factor authentication (2FA/MFA) for your Juniper Secure Access SSL VPN is now complete.
If you have other questions, contact Protectimus customer support service.
Protectimus Ltd
Carrick house, 49 Fitzwilliam Square,
Dublin D02 N578, Ireland
Ирландия: +353 19 014 565
США: +1 786 796 66 64
Protectimus Ltd
Carrick house, 49 Fitzwilliam Square,
Dublin D02 N578, Ireland
Ирландия: +353 19 014 565
США: +1 786 796 66 64


