Программируемый TOTP-токен в формате карты, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой SHA-1
Программируемый TOTP-токен в формате брелока, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой алгоритма SHA-256
Программируемый TOTP-токен в формате карты, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой SHA-1
Программируемый TOTP-токен в формате брелока, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой алгоритма SHA-256
Бесплатное 2FA-приложение с облачным бэкапом, удобным переносом токенов на новый телефон, PIN-кодом и биометрической защитой
Бесплатная доставка OTP с помощью чат-ботов в мессенджерах
Доставка одноразовых паролей через SMS
Бесплатная доставка OTP на email
Бесплатная доставка одноразовых паролей через push-уведомления
Бесплатное 2FA-приложение с облачным бэкапом, удобным переносом токенов на новый телефон, PIN-кодом и биометрической защитой
Бесплатная доставка OTP с помощью чат-ботов в мессенджерах
Доставка одноразовых паролей через SMS
Бесплатная доставка OTP на email
Бесплатная доставка одноразовых паролей через push-уведомления
Инструкции
В этом руководстве показано, как настроить двухфакторную аутентификацию для сетевой техники Cisco с помощью Облачного сервиса двухфакторной аутентифиции Protectimus или локальной 2FA платформы Protectimus.
Система двухфакторной аутентификации Protectimus взаимодействует с сетевым оборудованием Cisco по протоколу RADIUS. Компонент Protectimus RADIUS Server выступает в роли RADIUS-сервера. Он принимает входящие запросы на аутентификацию по протоколу RADIUS, обращается к хранилищу пользователей (Active Directory и т. д.) для проверки логина и пароля, а затем обращается к серверу двухфакторной аутентификации Protectimus для проверки одноразового пароля. Если оба фактора аутентификации верны, RADIUS-сервер Protectimus разрешает пользователю подключиться к сетевому коммутатору или свитчу Cisco.
Схема работы решения Protectimus для двухфакторной аутентификации при подключении к сетевой технике Cisco представлена на рисунке.
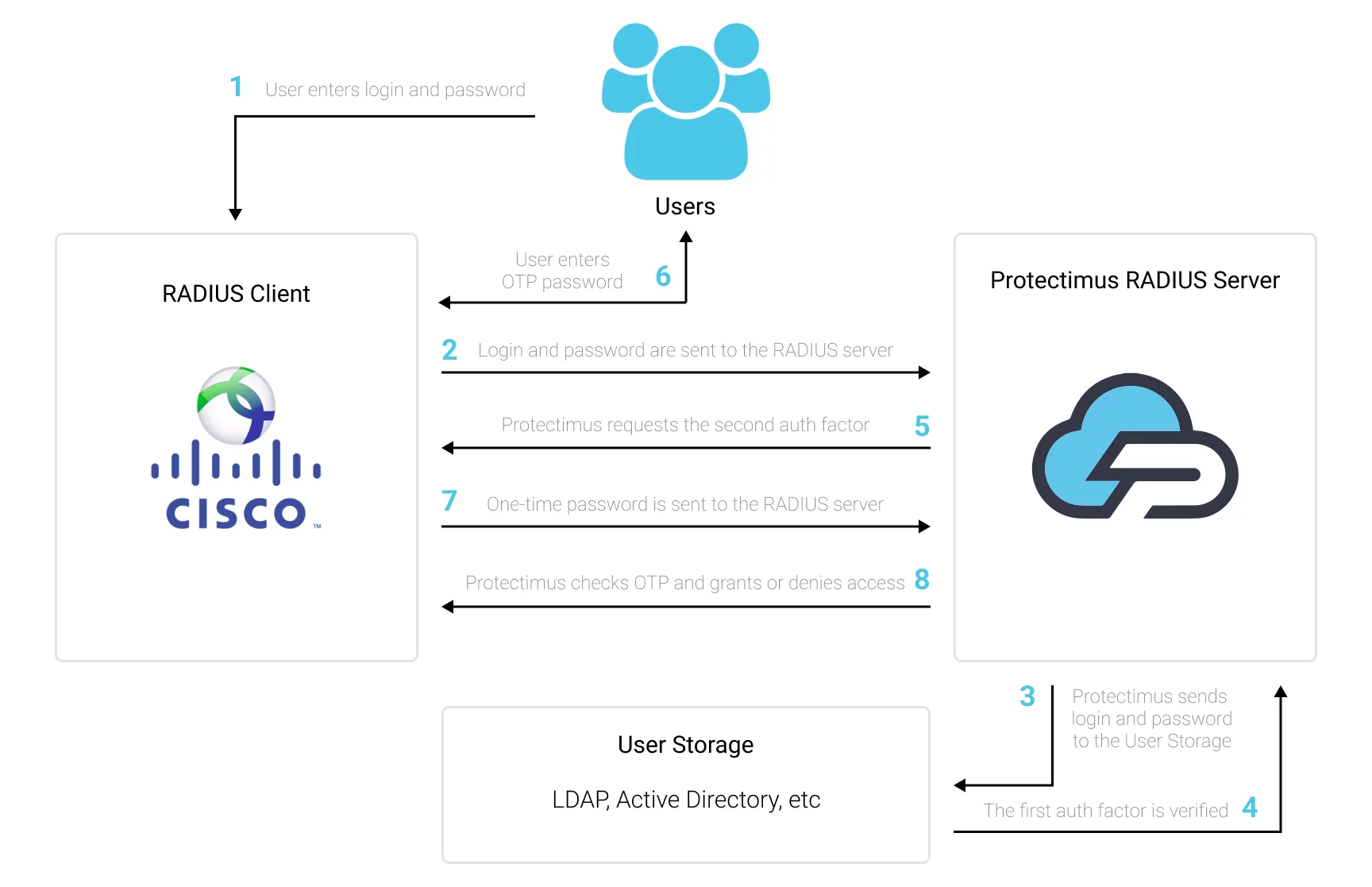
После настройки двухфакторной аутентификации для коммутаторов Cisco, чтобы подключиться к сетевой технике Cisco, пользователи будут вводить два разных фактора аутентификации.
После того, как вы активируете двухфакторную аутентификацию (2FA) для коммутаторов Cisco, взломать доступ к сетевой технике Cisco станет осень сложно. Заполучить оба фактора аутентификации одновременно практически невозможно. Более того, время действия одноразового пароля составляет всего 30 секунд, поэтому у злоумышленника будет слишком мало времени, чтобы взломать второй фактор.
Двухфакторная аутентификация (2FA / MFA) — это эффективная мера защиты от таких угроз кибербезопасности, как фишинг, социальная инженерия, брутфорс, кейлоггинг, атаки человек-посередине, подмена данных и т.д.
Интеграция двухфакторной аутентификации Protectimus с сетевой техники Cisco возможна по протоколу RADIUS:
- Зарегистрируйтесь в Облачном сервисе двухфакторной аутентификации или установите Локальную платформу Protectimus и задайте базовые настройки.
- Установите и настройте компонент Protectimus RADIUS Server.
- Настройте политики аутентификации на сетевом устройстве Cisco.
Подробные инструкции по установке и настройке Protectimus RADIUS Server доступны в Руководстве по установке и настройке Protectimus RADIUS Server.
Switch(config) #radius server [configuration-name]
Switch(config-radius-server) #address ipv4 hostname [auth-port integer] [acct-port integer]
Switch(config-radius-server) #key [shared-secret]Switch(config) #aaa group server radius [group-name]
Switch(config-sg-radius) #server name [configuration-name]Switch(config) #aaa authentication login [default | list-name] group [group-name] localНастройка двухфакторной аутентификации для коммутаторов Cisco завершена.
Если у вас есть вопросы, обратитесь в службу поддержки клиентов Protectimus.
Protectimus Ltd
Carrick house, 49 Fitzwilliam Square,
Dublin D02 N578, Ireland
Ирландия: +353 19 014 565
США: +1 786 796 66 64
Protectimus Ltd
Carrick house, 49 Fitzwilliam Square,
Dublin D02 N578, Ireland
Ирландия: +353 19 014 565
США: +1 786 796 66 64


