Программируемый TOTP-токен в формате карты, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой SHA-1
Программируемый TOTP-токен в формате брелока, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой алгоритма SHA-256
Программируемый TOTP-токен в формате карты, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой SHA-1
Программируемый TOTP-токен в формате брелока, совместимый с любой системой аутентификации
Классический аппаратный TOTP токен с поддержкой алгоритма SHA-256
Бесплатное 2FA-приложение с облачным бэкапом, удобным переносом токенов на новый телефон, PIN-кодом и биометрической защитой
Бесплатная доставка OTP с помощью чат-ботов в мессенджерах
Доставка одноразовых паролей через SMS
Бесплатная доставка OTP на email
Бесплатная доставка одноразовых паролей через push-уведомления
Бесплатное 2FA-приложение с облачным бэкапом, удобным переносом токенов на новый телефон, PIN-кодом и биометрической защитой
Бесплатная доставка OTP с помощью чат-ботов в мессенджерах
Доставка одноразовых паролей через SMS
Бесплатная доставка OTP на email
Бесплатная доставка одноразовых паролей через push-уведомления
Инструкции
В этом руководстве показано, как настроить двухфакторную аутентификацию (2FA/MFA) для Pulse Connect Secure SSL VPN с помощью решения многофакторной аутентификации Protectimus.
Система двухфакторной аутентификации Protectimus интегрируется с Pulse Connect Secure SSL VPN через протокол аутентификации RADIUS.
В этом сценарии Облачный сервис двухфакторной аутентификации или Локальная платформа Protectimus выступает в качестве RADIUS-сервера, а Pulse Connect Secure SSL VPN берет на себя роль RADIUS-клиента.
Схема работы решения Protectimus для двухфакторной аутентификации в Pulse Connect Secure SSL VPN представлена ниже.
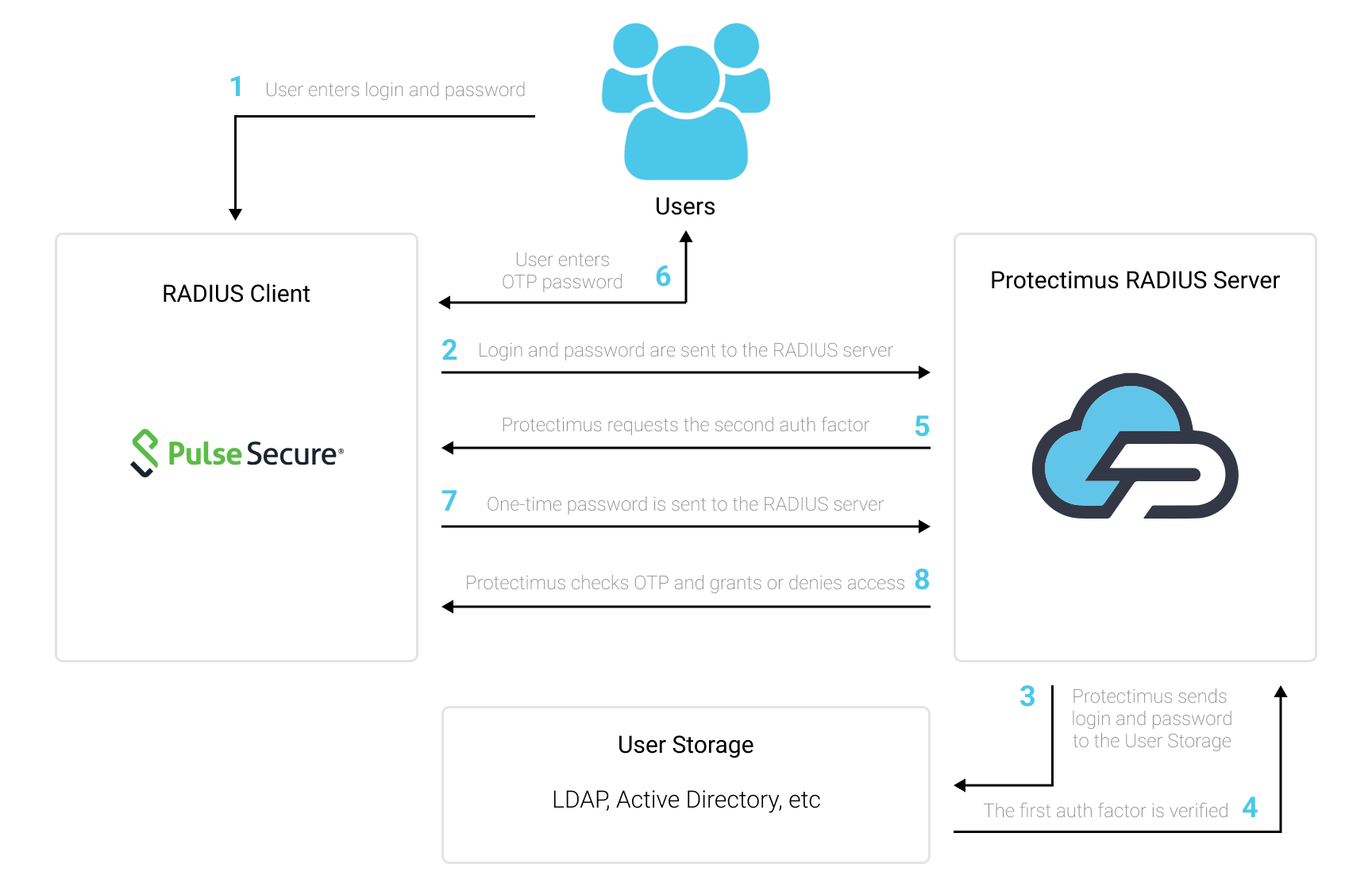
Двухфакторная аутентификация (2FA/MFA) защищает учетные записи пользователей Pulse Connect Secure SSL VPN от фишинга, брутфорса, кейлоггеров, атак «человек посередине», подмены данных, социальной инженерии и других подобных хакерских приемов.
После того как вы подключите двухфакторную аутентификацию, чтобы войти в свои учетные записи, пользователи Pulse Secure VPN будут использовать два разных фактора аутентификации.
Чтобы взломать учетную запись Pulse Connect Secure SSL VPN, защищенную двухфакторной аутентификацией, хакеру нужны оба фактора одновременно. Более того, у хакера есть всего 30 секунд, чтобы взломать и использовать одноразовый пароль на основе времени. Выполнить эти условия практически невозможно, что и делает двухфакторную аутентификацию такой эффективной.
Интеграция двухфакторной аутентификации Protectimus с Pulse Connect Secure SSL VPN возможна по протоколу RADIUS:
- Зарегистрируйтесь в Облачном сервисе двухфакторной аутентификации или установите Локальную платформу Protectimus и задайте базовые настройки.
- Установите и настройте компонент Protectimus RADIUS Server.
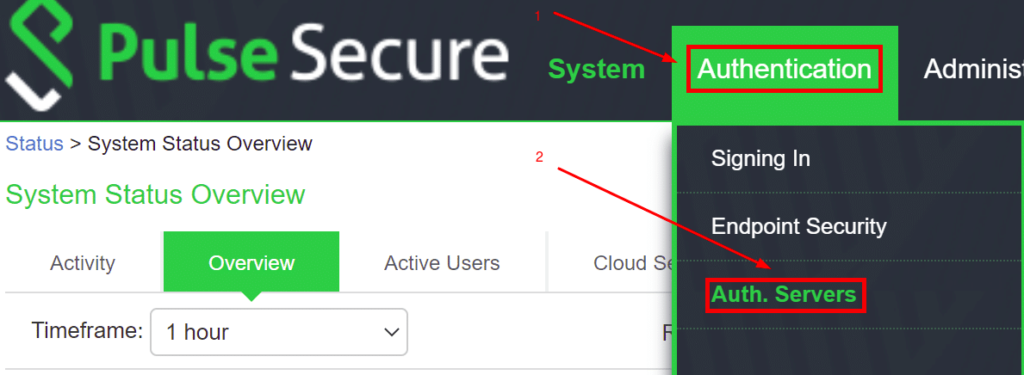
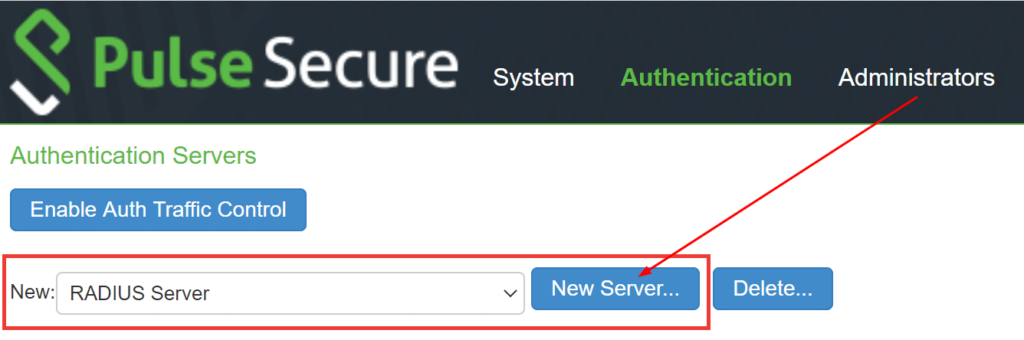
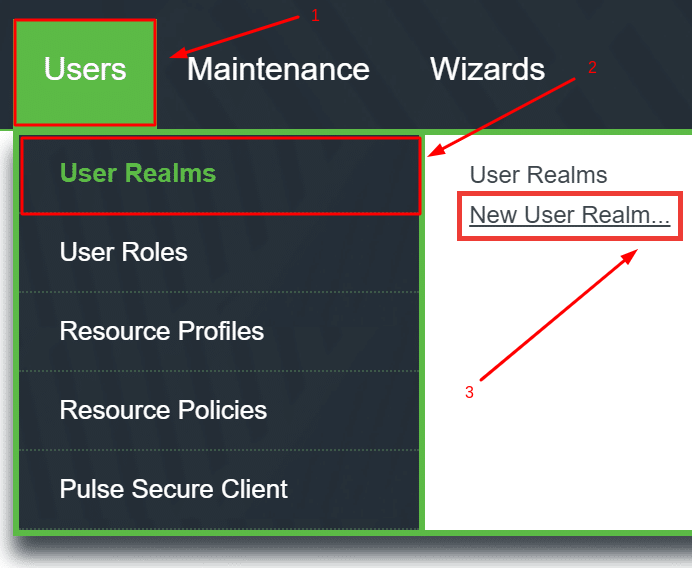
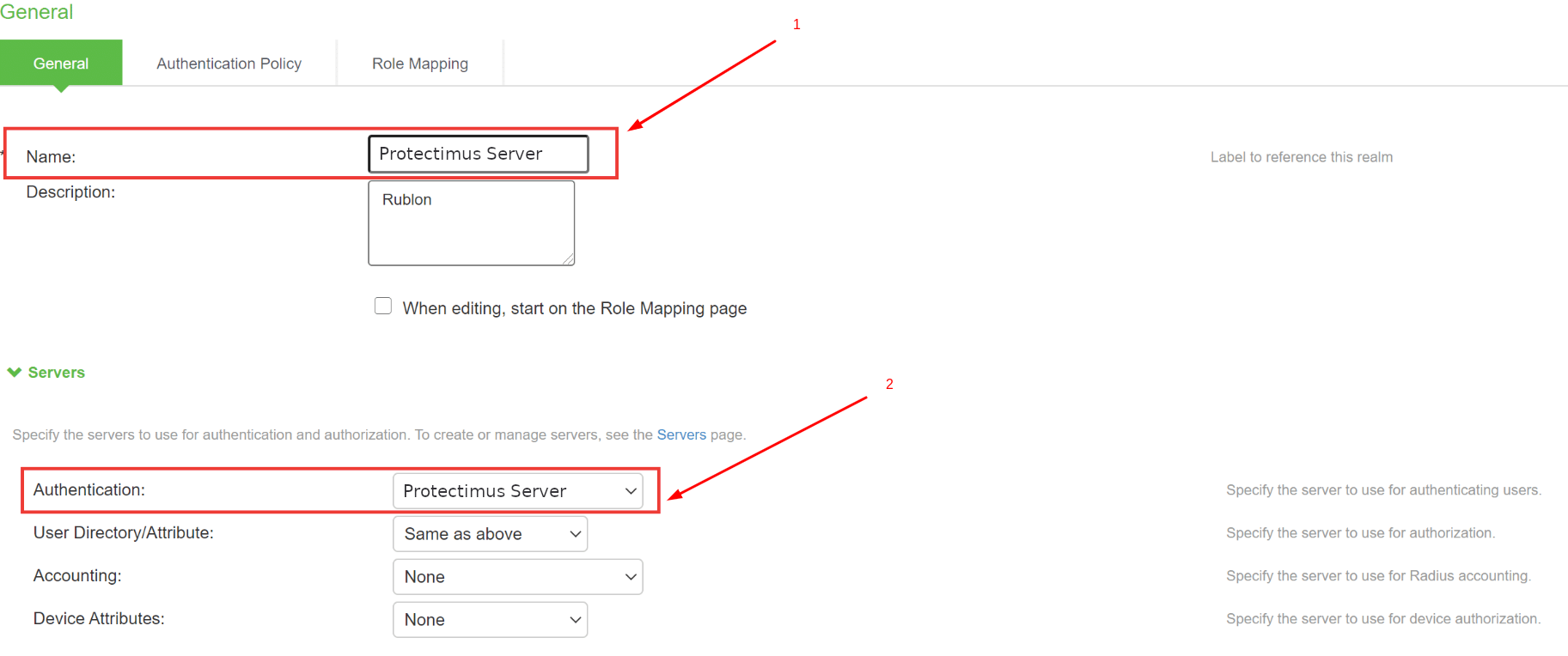
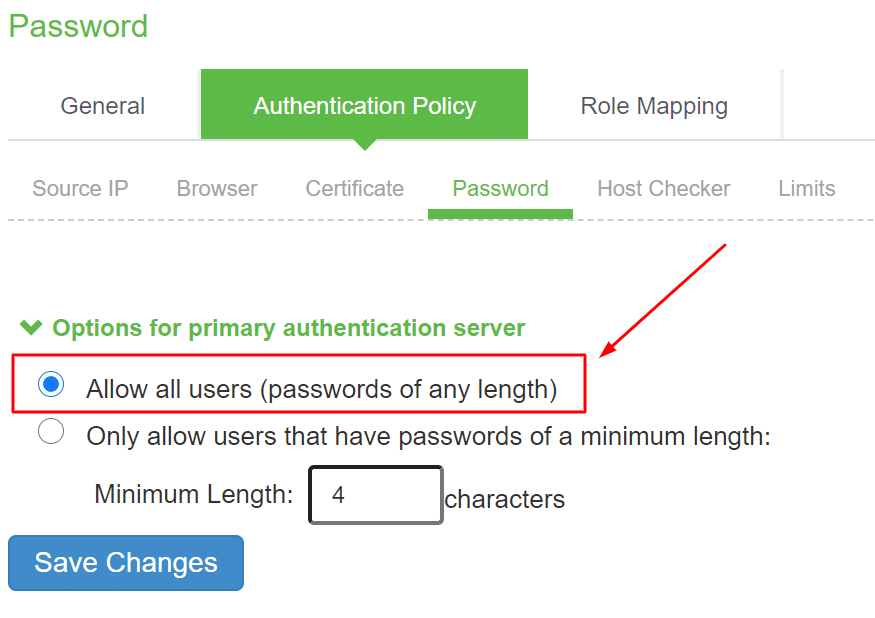
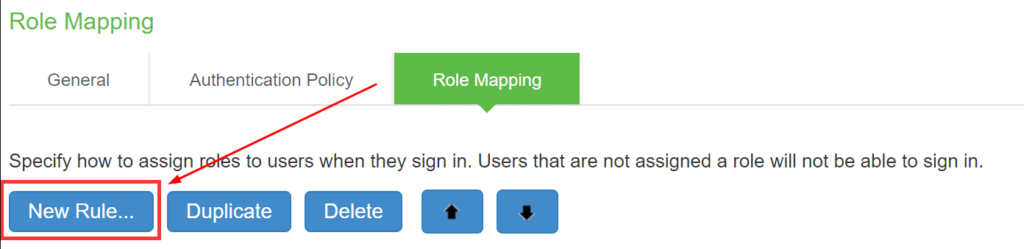
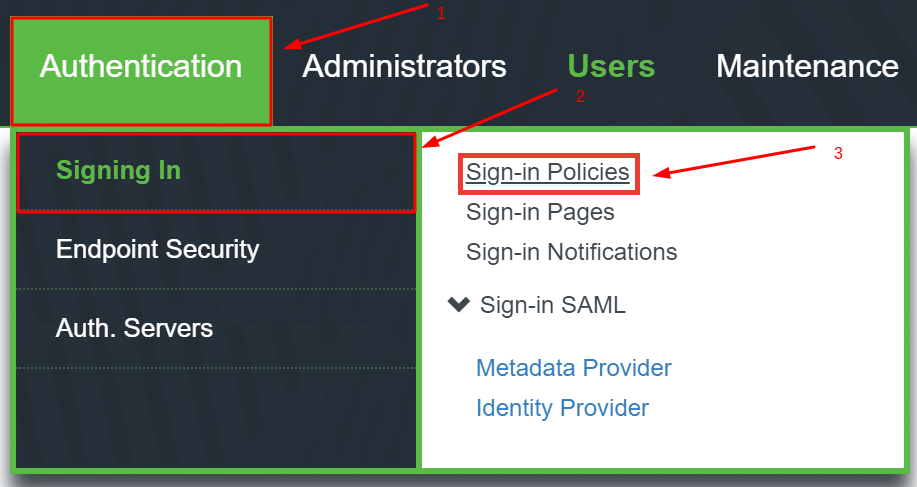
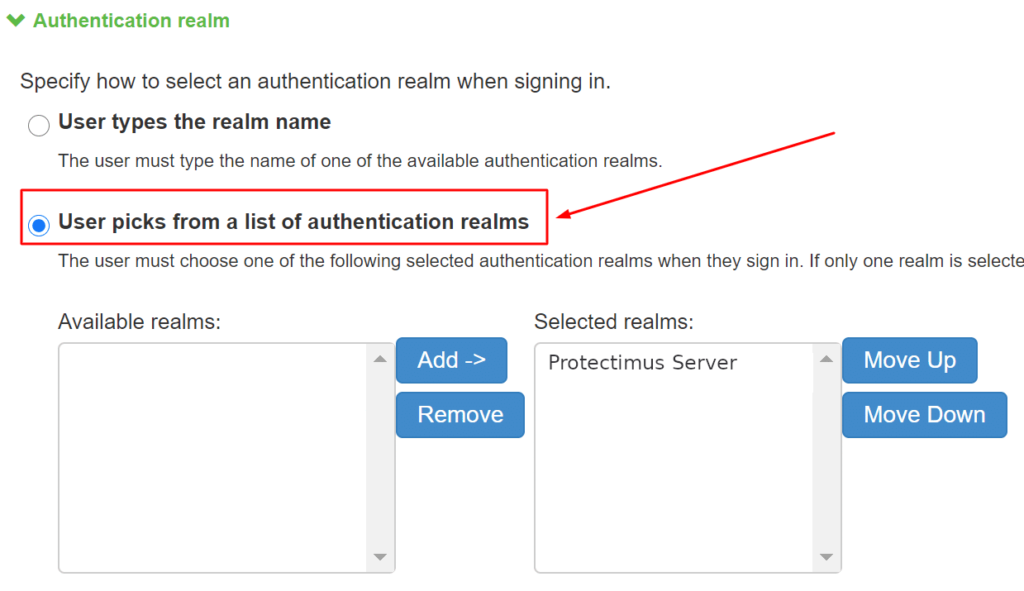
- Настройте политики аутентификации в Pulse Connect Secure SSL VPN.
Подробные инструкции по установке и настройке Protectimus RADIUS Server доступны в Руководстве по установке и настройке Protectimus RADIUS Server.
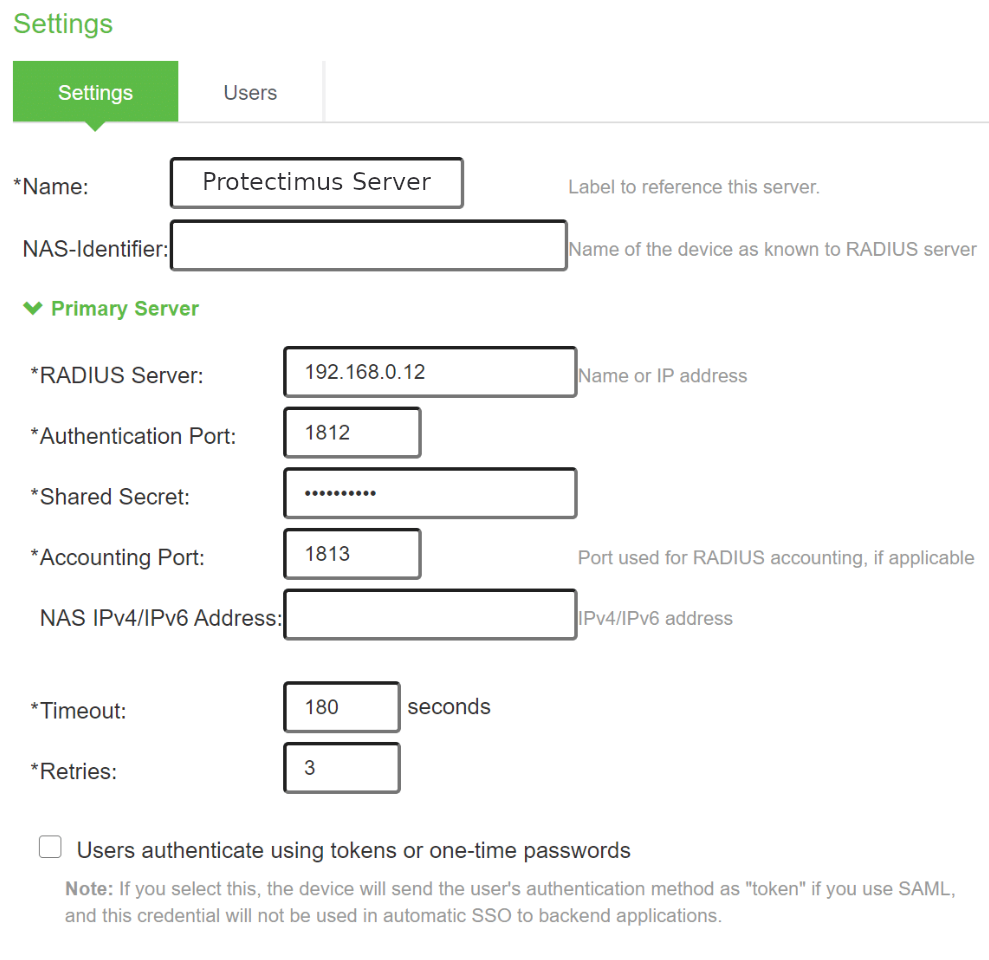
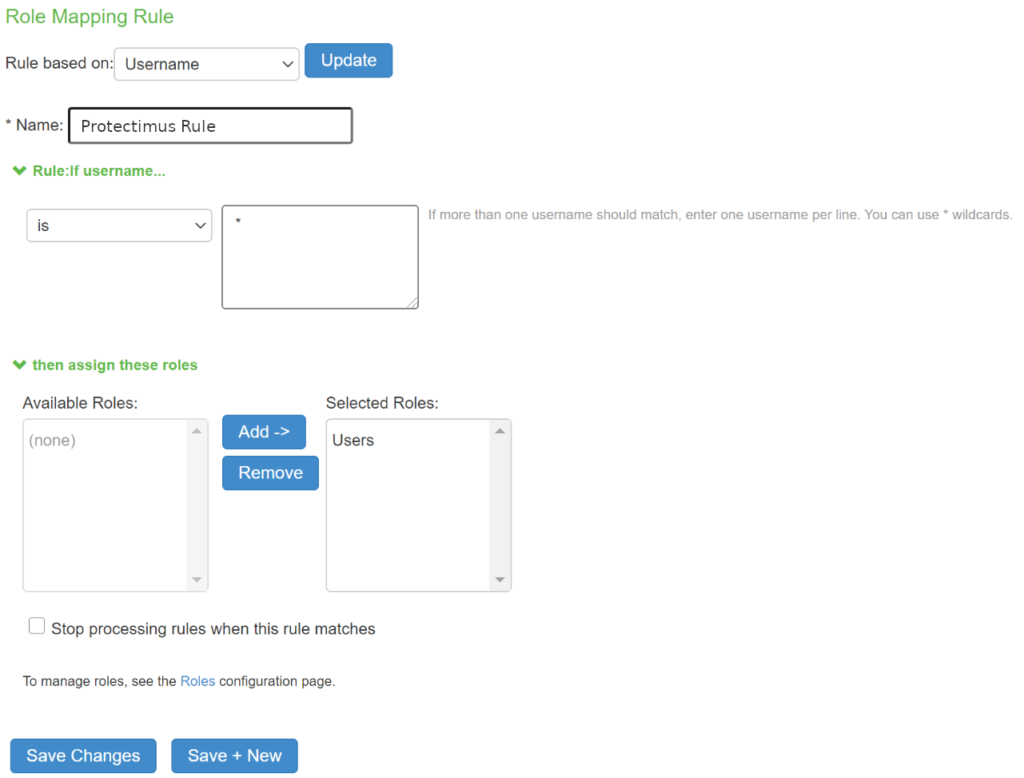
| Name | Придумайте имя для своего RADIUS-сервера, например, Protectimus Server. |
| RADIUS Server | Введите IP-адрес сервера, на котором установлен компонент Protectimus RADIUS Server. |
| Authentication Port | Укажите 1812 (или тот порт, который вы указали в файле Protectimus radius.yml при настройке Protectimus RADIUS Server). |
| Shared Secret | Укажите созданный вами секретный ключ в файле Protectimus radius.yml (свойство radius.secret). |
| Timeout | Установите значение 180 секунд. |
| Retries | Установите значение 3. |
Интеграция двухфакторной аутентификации в Pulse Connect Secure SSL VPN завершена.
Если у вас есть вопросы, обратитесь в службу поддержки клиентов Protectimus.
Protectimus Ltd
Carrick house, 49 Fitzwilliam Square,
Dublin D02 N578, Ireland
Ирландия: +353 19 014 565
США: +1 786 796 66 64
Protectimus Ltd
Carrick house, 49 Fitzwilliam Square,
Dublin D02 N578, Ireland
Ирландия: +353 19 014 565
США: +1 786 796 66 64


